
Why perform a Risk Assessment?
- Risk assessments are a critical stage of the security management process for any business, organisation, person, or venue.
- Risk assessments are the keystone in effective protective security and cybersecurity planning.
- They require a high level of security expertise and attention to detail.

What is a Risk Assessment?
A security risk assessment involves a formal assessment of the risks and threats companies, organisations, venues, or people may face, as many regulations, corporate policies and standards require.
Methods for professional security risk assessments are relatively well defined, but not every security consultant is familiar with them.
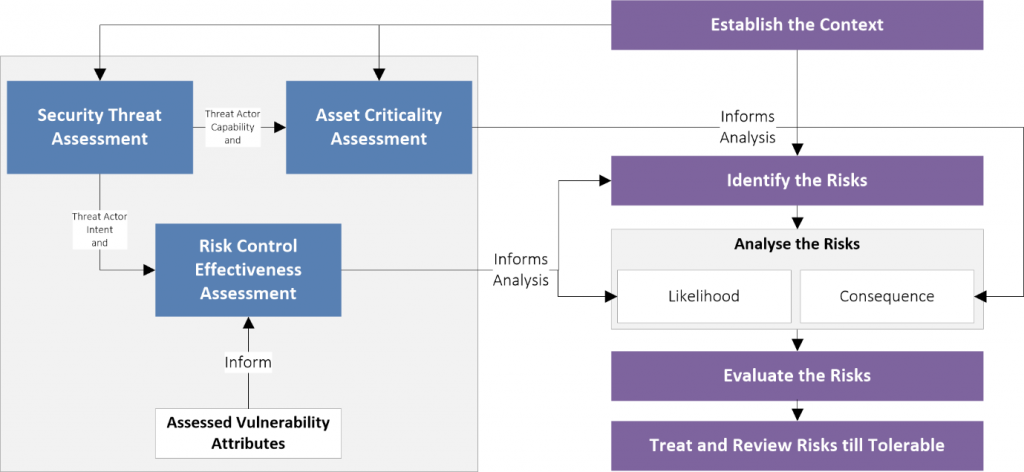
Industry Risk’s assessments consider the client’s unique scope and context, their assets and their criticality, threats, vulnerabilities, controls and risks.
A risk assessment also involves a greater degree of effort than a security review. The latter is usually a direct review of the effectiveness of security measures and is usually based on an assessor’s subjective viewpoint.
Example Risk Assessment Tools
Industry Risk has created SECTARA, a market leading security risk assessment platform to assist security consultants and security managers produce high-quality risk assessments.
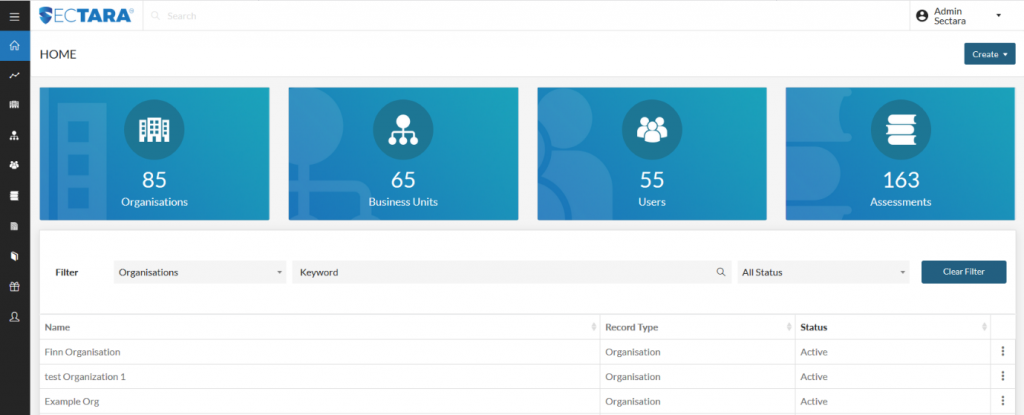
SECTARA requires practitioners to adhere to a high-quality methodology during the assessment process, while allowing for unique contextual arrangements to be factored into the process. It also enables excellent past intellectual property to be stored in libraries and repurposed to maximise the assessor’s productivity.
Risk Assessment Process
Industry Risk’s process for assessments is well documented within our articles and security news, and via the myriad of risk assessments that we’ve completed over many years.
Our assessments consider scope and context, assets and their criticality, threats, vulnerabilities, risk controls and risks.
A key strength in our assessment process lies in ensuring pragmatic implementable recommendations. We avoid unrealistic suggestions that do not meet cost-benefit considerations. This approach gives confidence when presenting and discussing recommendations with senior management.
Our assessment philosophy at Industry Risk is straight-forward:
Equipped with a clear view of the risks facing your organisation, you’re better positioned to harmonise security programs and plan risk business cases in a way that assures stakeholder support and gets them implemented.
In conducting risk assessments, we strongly believe:
- Agree End-State Planning: Client expectations on the shape and form of deliverables must be clearly understood to ensure outcomes meet expectations.
- Document Context: Assessment context must be documented in detail to lay foundations for later stages, including External, Internal and Security Risk Context.
- Identify Assets: Identifying and assessing the relative criticality of in-scope assets is key to assessing risk.
- Describe Threats: Describing the nature of the threats realistically and clearly for the client is a pivotal part of the process.
- Identify Vulnerability and Controls: Individual security controls and vulnerabilities are identified and assessed, based on the scope of the assignment.
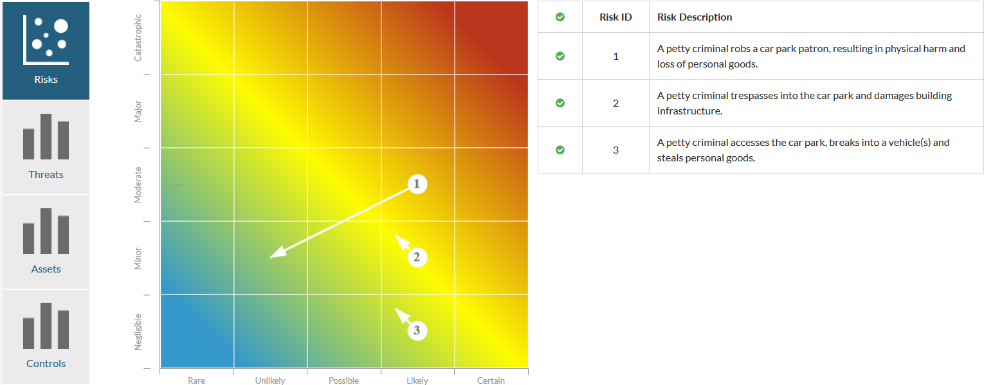
- Document Risks: Risks are documented in detail within a Risk Register, assessed for tolerability, treated, then assessed again for residual risk levels.
- Recommend Security Treatments: We recommend realistic security improvements based on our findings and the risks faced.
Overall, security risk assessments are critically important for businesses, organisation, people and venues to understand the threats that face them and to enable them to plan for managing and dealing with those security threats.
Our risk assessment software platform SECTARA facilitates how advanced threat assessments should be completed and illustrates Industry Risk’s commitment to best practice in security risk management and high-quality results. It also demonstrates our belief in the importance of this critical process in security management.
Contact Industry Risk to discuss how we can help improve your security or visit SECTARA to review our market-leading security software platform.
