Our Cybersecurity Model
Our Cybersecurity Services
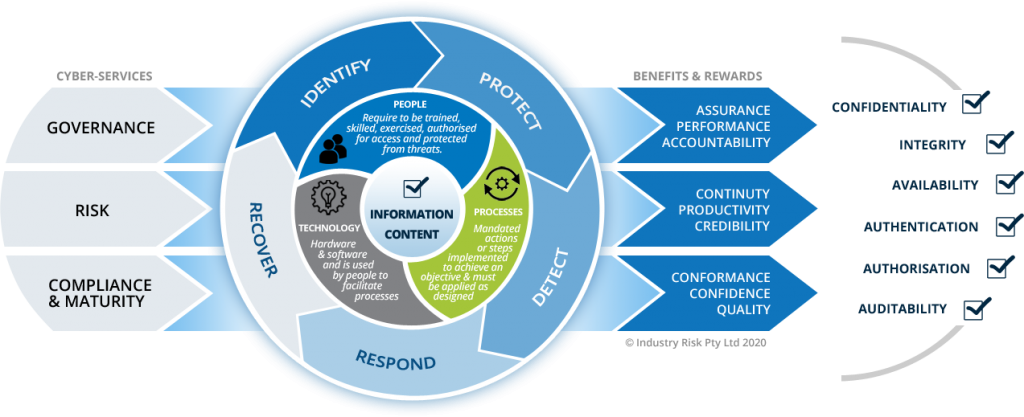
Effective cybersecurity strategies encompass governance, risk and compliance functions to guide, direct and manage people, processes and technologies. Events continually prove that not getting the design, blend or quality right can be disastrous for organisations. So when your business demands a high level of confidence that information is managed and assured effectively, trust Industry Risk to be your cybersecurity partner of choice…
Governance
Cybersecurity governance encompasses a range of documented arrangements, and should always underpin business objectives and be part of an integrated system. Industry Risk’s approach to cyber-governance ensures that our services are always tied to clear objectives, and that any documentation created accounts for dependencies and knock-on effects that it may cause.
We always seek to minimise content for simplicity, and ensure that arrangements are understood prior to finalising initial project stages.
Cyber-Governance Services
- Policies, plans and instructions
- Cybersecurity frameworks
- ISM/NIST documentation
- ISO 27001 alignment

Risk
Cybersecurity risk assessments should be performed prior to initial system design processes, and iterated (continually) thereafter. Formal triggers should also be defined within each organisation’s risk frameworks, to indicate the conditions under which assessments should be carried out (e.g. prior to any network changes).
Industry risk developed SECTARA (Security Threat and Risk Assessor) specifically for this purpose. Based on ISO 31000 – Risk management, directly aligned to ISO 27005 – Information SRM, and in-sync with NIST SP 800-37, our security risk assessments identify and enable business leaders to manage extant risks, while remaining vigilant to emerging ones.
Cyber-Risk Services
- Risk management frameworks
- Risk assessments & monitoring
- ISO 31000, 27005 and NIST SP 800-37
- Cyber-risk training & mentoring
- Retained risk services
- Network vulnerability scans

Compliance & Maturity
While organisations fend off threat acts from a myriad of risk-assessed cyber-actors, many are also obliged by legislation to comply with prescriptive controls for information security assurance. In doing so, a trend has developed to allow for maturity assessments in order to mitigate against a one-size-fits-all approach to mandatory controls.
Industry Risk are expert in both forms of assessments, and are intimate with various baseline criteria, including ISO 27001, the Commonwealth Information Security Manual (ISM) and NIST etc. Our reports encourage an approach that mirrors major management system standards and includes provisions to Plan, Do, Check, Act (PDCA) throughout the cybersecurity management lifecycle, as illustrated here.
Cyber-Assurance Services
- Compliance/Maturity assessments
- Privacy (IPPs) & GDPR auditing
- IRAP compliance assessments
- Gap Analyses & benchmarking
- 3rd Party Auditing
- PDCA Assessment & Development







